Making complex Security Access policies clearer, more scalable, and safer to manage.
F5 Networks
BIG-IP Next Central Manager 2024
Sole Product Designer

Case Study
My Role: Sole Product Designer
Global Team: 3 PMs (US), 3 Engineering Teams (US, Israel, India)
Scope: Policy creation, visual editor, config workflows, 3rd-party integration
My impact
Reduced complex policy creation from hours to minutes
Lowered configuration risk in a security-critical platform
Simplified complex security workflows through visual policy modeling
Enabled scalable policy reuse across hundreds of applications
Delivered a MVP production-ready editor under aggressive timelines
Summary
I led the redesign of access policy authoring for F5’s Zero Trust platform. The legacy editor was powerful but difficult to understand, making policies slow to create and risky to modify.
I introduced a visual policy system built on reusable components and structural guardrails, transforming fragile configuration into a clear, composable workflow.
The result was a production-ready Visual Policy Designer that accelerated policy creation, reduced configuration risk, and preserved trusted customer workflows.

The Problem
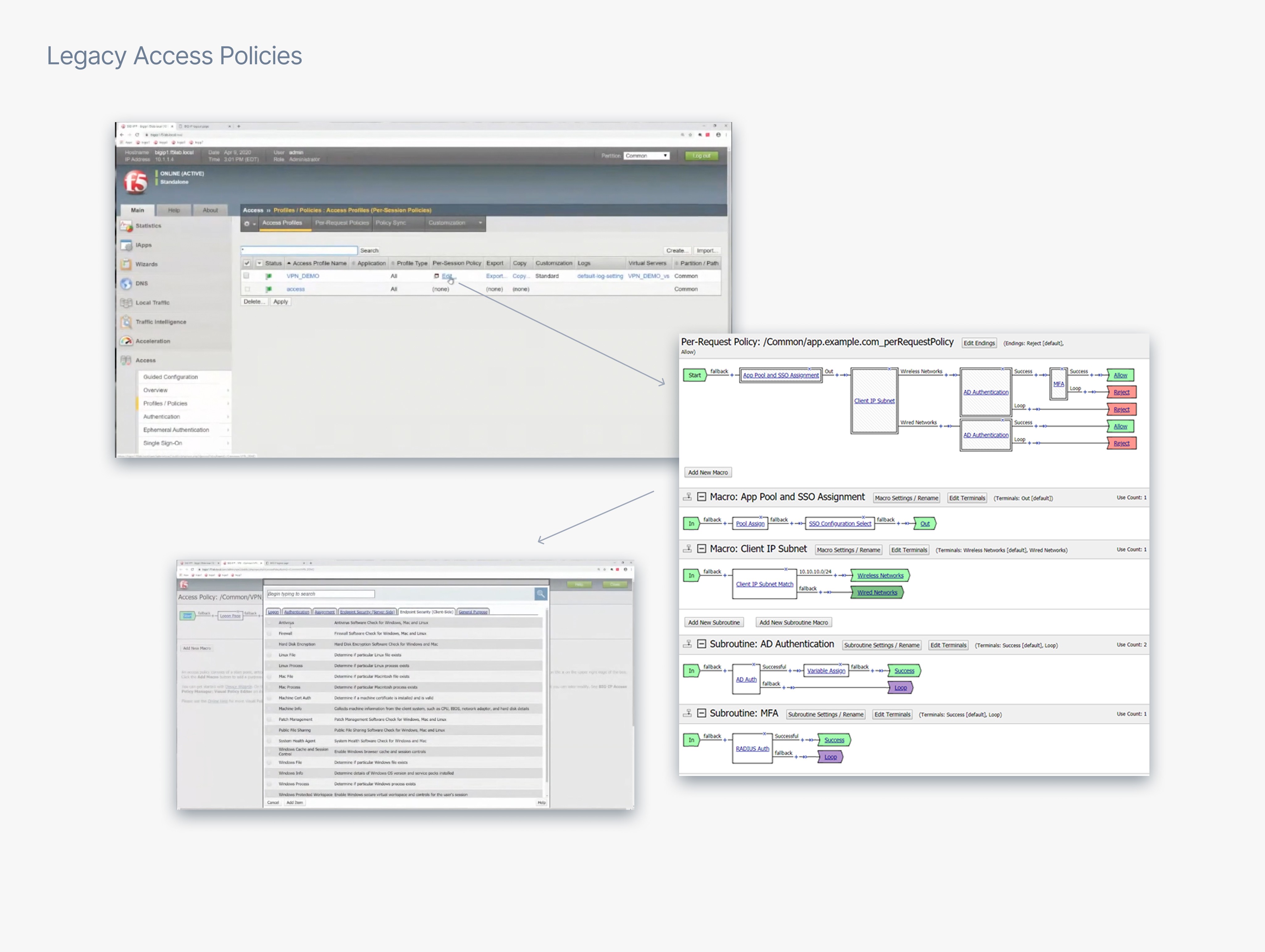
Managing Access policies in the legacy system was slow and difficult to understand.
As policies grew more complex:
Policy logic became hard to follow
The interface did not scale visually
Small configuration changes introduced security risks
Reusing policies across applications was nearly impossible
The legacy editor exposed system complexity instead of helping administrators understand policy behavior.
The challenge was to simplify policy creation while preserving familiar workflows used by existing customers.
The Goal
Design a clear, scalable policy authoring experience
Make complex policy logic easy to visualize
Reduce effort required to create and modify policies
Minimize configuration risk in a security-critical environment
Enable reuse across hundreds or thousands of applications
Feel modern, intuitive, and reliable for administrators
Solution
Design a composable policy system
I designed a Visual Policy Designer that transformed policy creation from fragile configuration into a clear, composable workflow.
Key capabilities included:
Component-based policy building blocks
Structural guardrails preventing invalid configurations
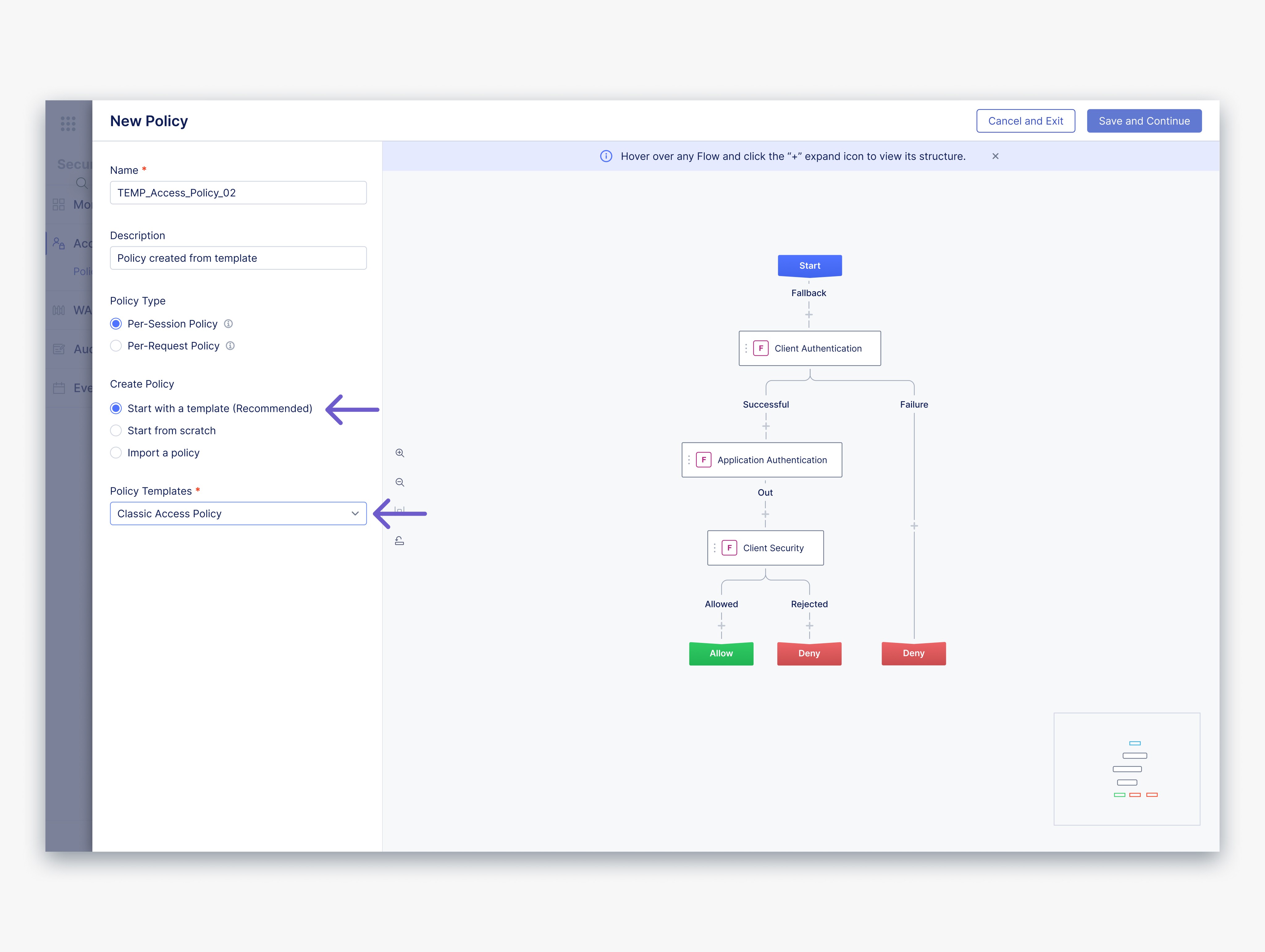
Reusable templates for faster policy creation
Policies treated as first-class system objects for reuse across applications
Security Admins could now visualize policy logic and compose policies with confidence.



Product & Design Leadership
Defining the policy authoring model
I evaluated the legacy experience to identify strengths and friction points, then defined the ideal policy authoring model and aligned Product and Engineering around a solution that balanced usability, technical constraints, and delivery timelines.
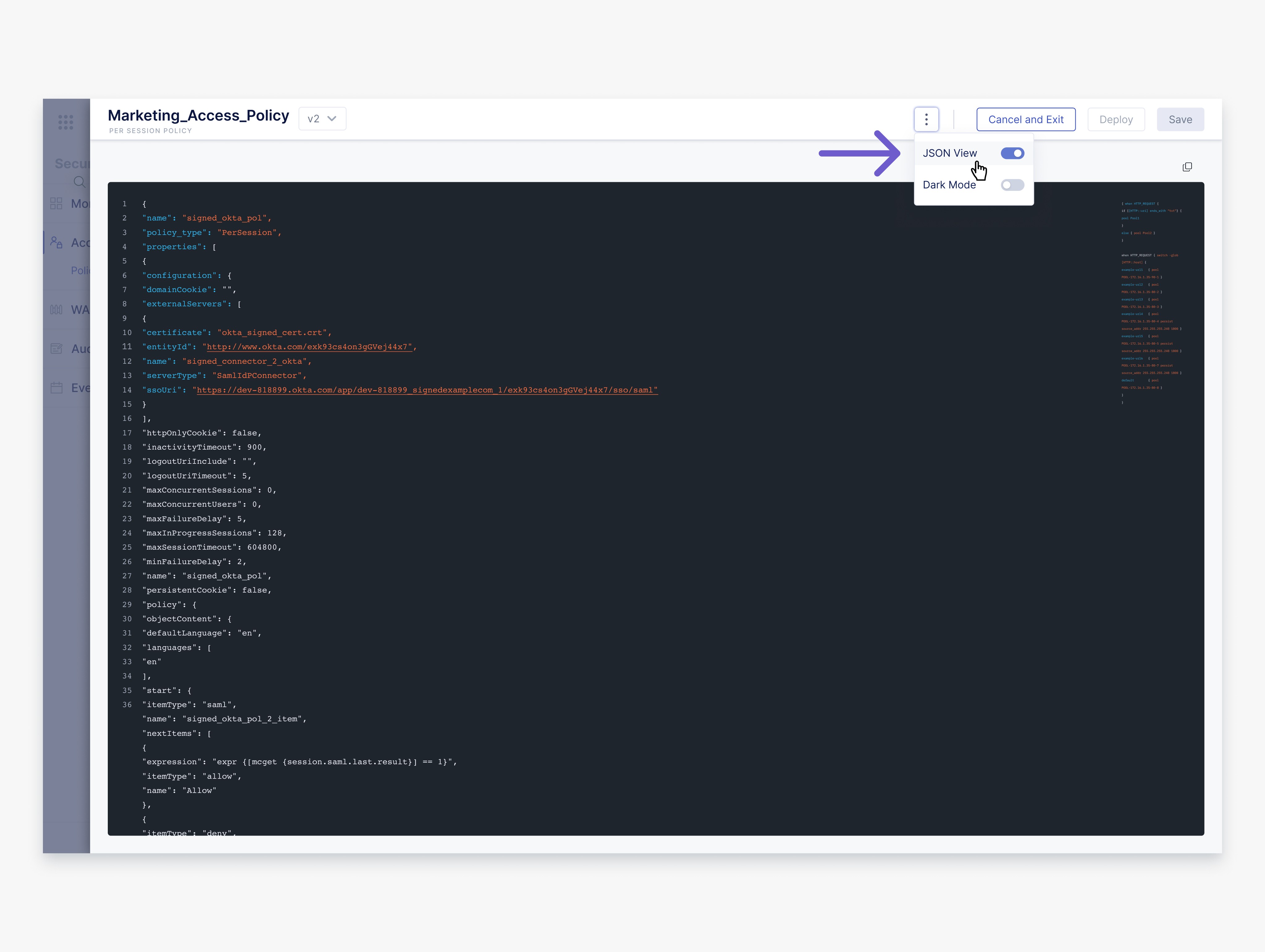
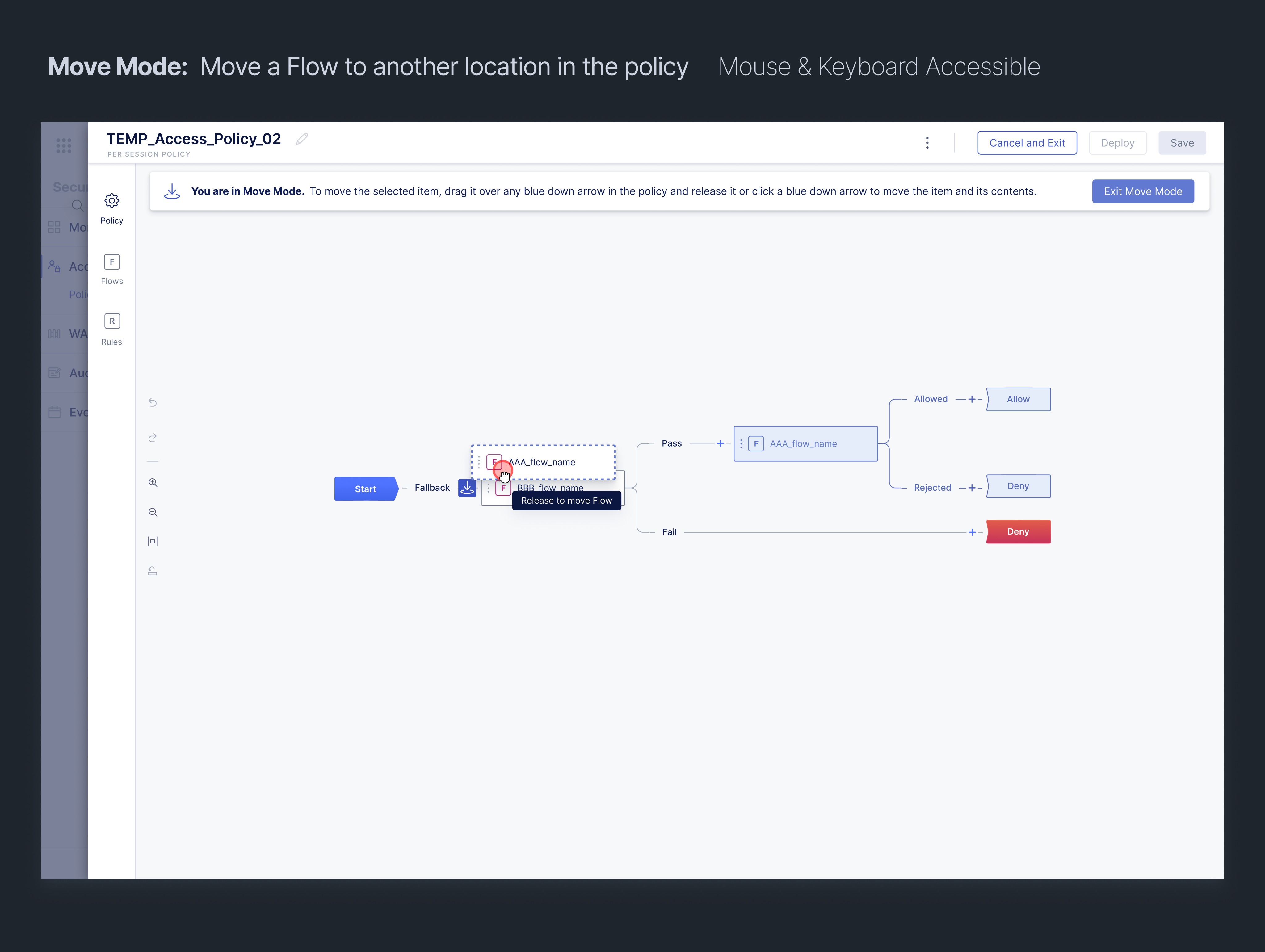
Defined the interaction model for visual policy authoring, simplifying complex logic into a composable workflow system
Partnered with Product Management to shape requirements and prioritize features
Validated multiple interaction models to identify the approach that reduced friction
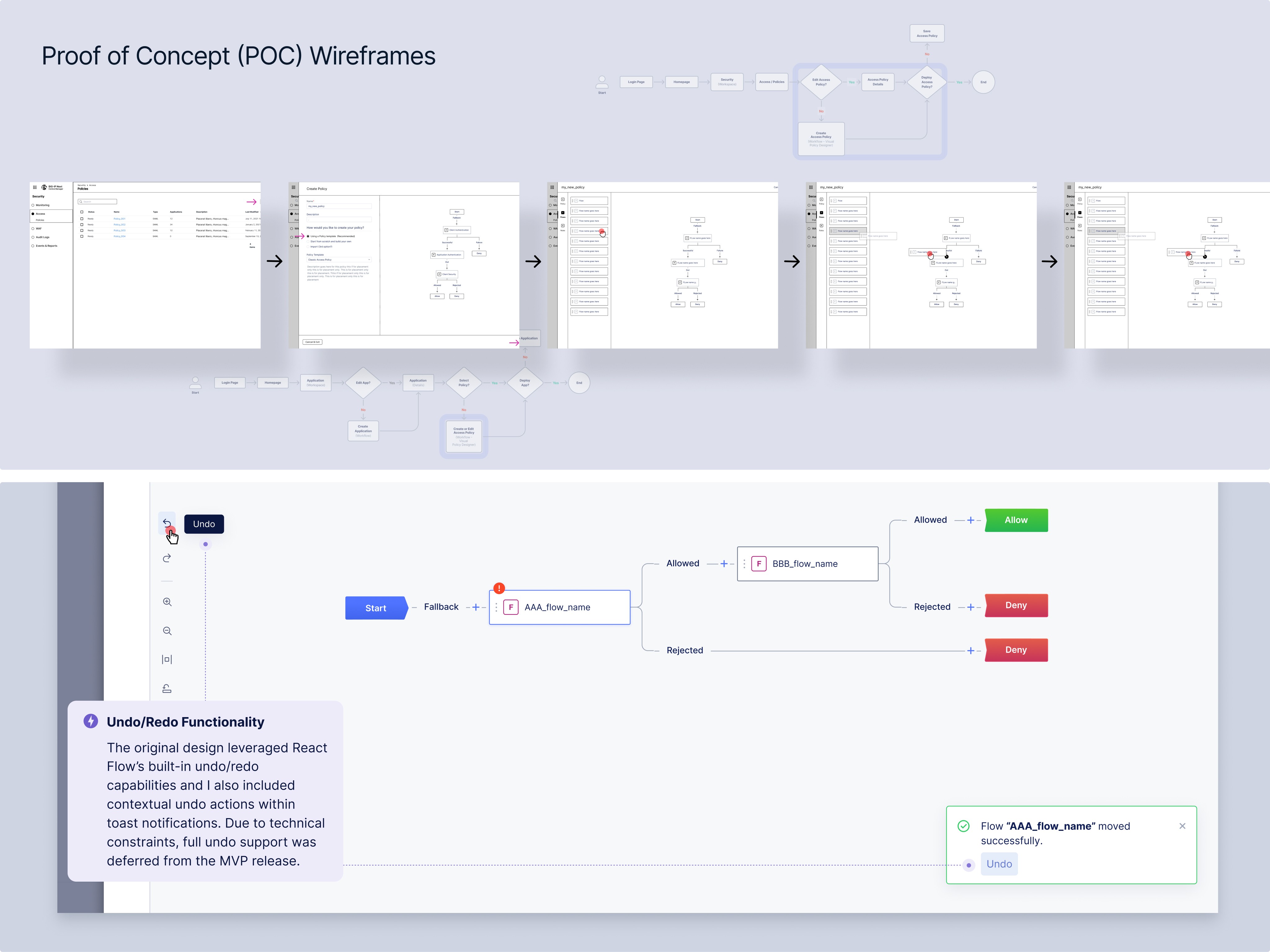
Led cross-functional evaluation of React Flow to support secure node-based editing
Worked closely with Engineering during implementation to balance clarity, feasibility, and speed to deliver
Constraints
Design improvements needed to respect the realities of a complex enterprise platform.
Modernize the experience without disrupting trusted production workflows
Complex state management and persistence requirements
Engineering already progressing from my early POC wireframes
Fixed technical architecture limiting implementation options
High reliability expectations due to the security-critical nature of the platform
To protect MVP stability, several requested features (such as undo/redo) were deferred.
Key Design Decisions
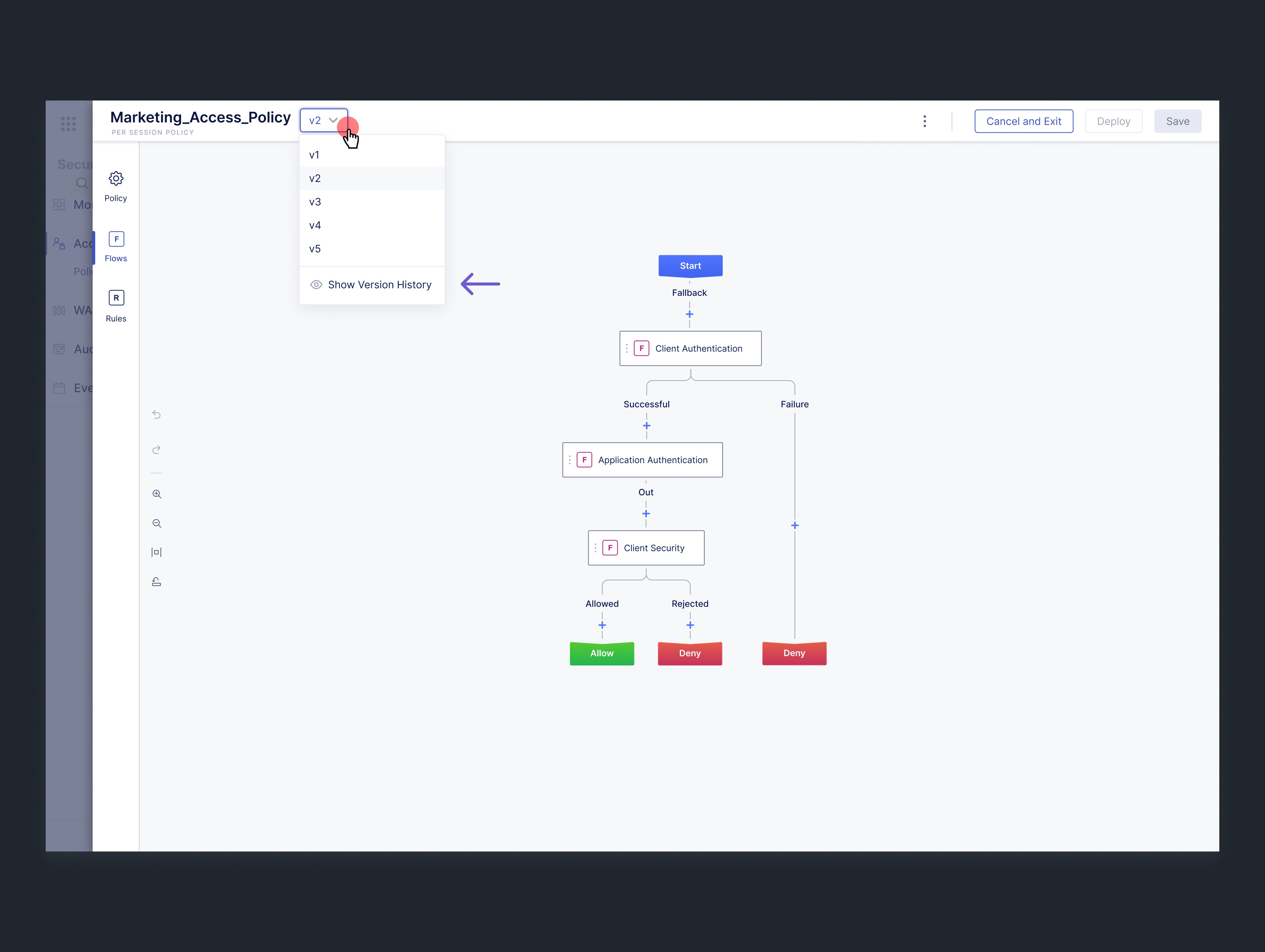
Visual policy modeling
Policies were represented as a node-based visual system instead of nested configuration forms, making complex logic easier to understand at a glance.
Modular policy components
Policies were built from reusable building blocks:
Flows
Rules
Subroutines
This modular structure reduced duplication and supported policy reuse across applications.
Structural guardrails
Built-in constraints prevented invalid configurations, reducing errors in production environments.
Policy templates
Reusable templates allowed administrators to quickly create common policy configurations, improving speed and consistency
Outcomes
Policy creation reduced from complex configuration to minutes
Cognitive load reduced through visual, contextual policy modeling
Configuration risk lowered through structural guardrails and system feedback
Scalable policy framework established across applications
Production-ready editor delivered under aggressive timelines
Ownership
As the sole designer, I:
Defined the end-to-end UX vision and interaction model
Influenced system architecture through design-first thinking
Designed the core editor workflows, enabling visual policy creation
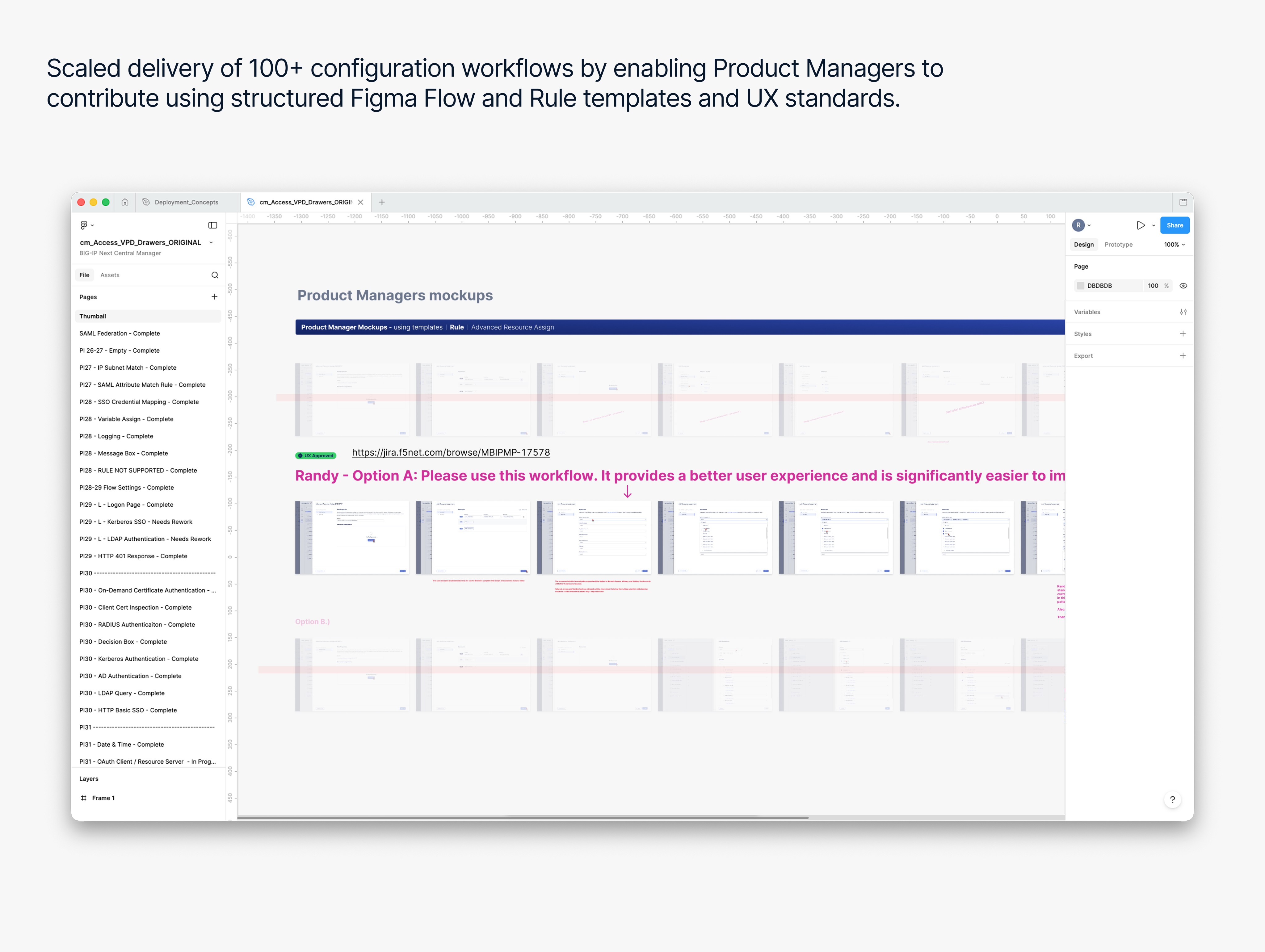
Established reusable patterns and templates for scalability
Scaled delivery of 100+ configuration pages by enabling PM contributions through Figma templates
Work in Parallel
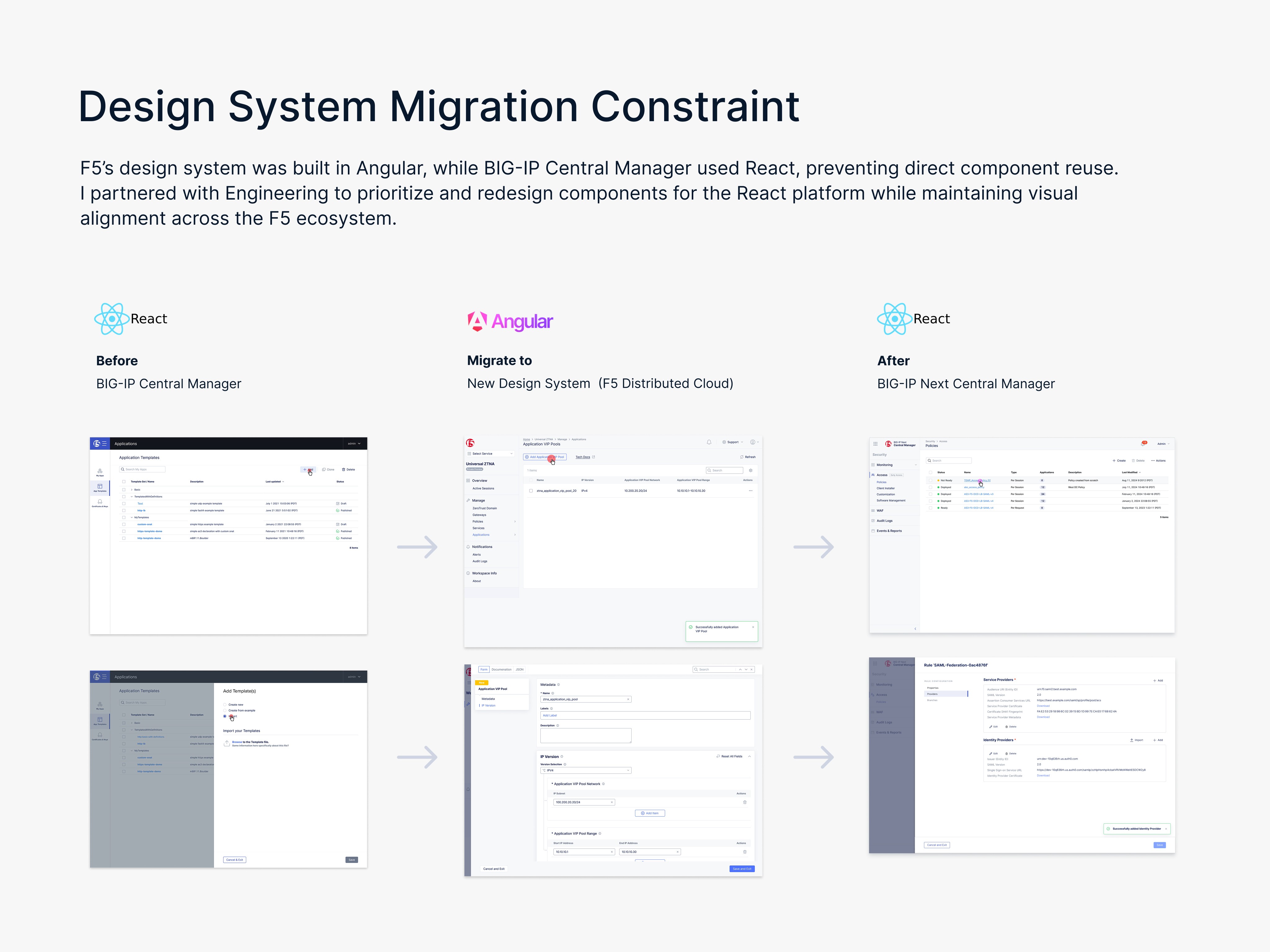
Design system transformation
While redesigning policy authoring, I also led the migration of BIG-IP Next Central Manager to F5’s unified design system.
This included:
Re-architecting information architecture and navigation
Modernizing components and design patterns
Aligning the visual experience with F5 Distributed Cloud and NGINX
Preserving stability for a mission-critical enterprise platform
technical constraints
F5’s design system was built in Angular, while Central Manager used React, preventing direct component reuse.
I partnered with Engineering to redesign components for React while maintaining alignment with the broader F5 ecosystem.
Future Opportunities
What i would do next
Policy version history and restore for safe rollback
Unified undo/redo state management
Seamless autosave during policy editing
In-product onboarding guidance for new administrators (Walk Me)
Expanded validation feedback to surface configuration issues earlier
AI-assisted scenario exploration to identify edge cases